Over the weekend, the Chaos Computer Club announced that it had bypassed Apple’s Touch ID sensor using a photograph of a fingerprint to create a fake fingerprint model.
The full fingerprint emulation process has now been detailed in a new video from CCC member Starbug and replicated by security expert Marc Rogers, who believes the average consumer has nothing to worry about.
As seen in the video, the CCC uses a fingerprint taken from the screen of the iPhone 5s and then uses a complicated multi-step process to convert it to a usable print. According to Starbug, who spoke to Ars Technica, the process "was way easier than expected," taking just 30 hours to complete.
I was very disappointed, as I hoped to hack on it for a week or two. There was no challenge at all; the attack was very straightforward and trivial.
The Touch ID is nevertheless a very reliable fingerprint system. However, users should only consider it an increase in convenience and not security.
While Starbug suggests that the hack is "very easy" and can be completed with "inexpensive office equipment like an image scanner, a laser printer, and a kit for etching PCBs," Marc Rogers, who also completed the bypass, disagrees, noting that it requires "over a thousand dollars worth of equipment."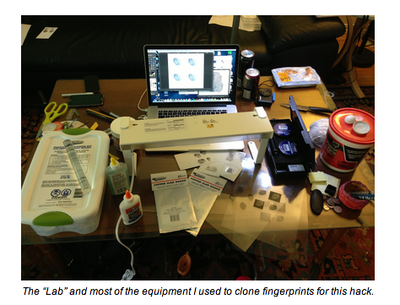
But, the reality is these flaws are not something that the average consumer should worry about. Why? Because exploiting them was anything but trivial.
Hacking TouchID relies upon a combination of skills, existing academic research and the patience of a Crime Scene Technician.
Rogers goes on to explain the process, which requires an unsmudged, complete print of the correct finger and a way to “lift” the print using cyanoacrylate (super glue) fumes, fingerprint powder, and fingerprint tape. The lifted fingerprint must then be photographed, edited, and printed onto transparency film, where it is converted to a usable fingerprint via a PCB board or a laser printer.
Even when all of these steps are created, using the fake fingerprint was "tricky" and prone to failure.
So what do we learn from all this?
Practically, an attack is still a little bit in the realm of a John le Carré novel. It is certainly not something your average street thief would be able to do, and even then, they would have to get lucky. Don’t forget you only get five attempts before TouchID rejects all fingerprints requiring a PIN code to unlock it.
However, let’s be clear, TouchID is unlikely to withstand a targeted attack. A dedicated attacker with time and resources to observe his victim and collect data, is probably not going to see TouchID as much of a challenge. Luckily this isn’t a threat that many of us face.
With Touch ID able to be bypassed through a fake fingerprint, it remains unclear how the system functions. According to Apple, the sensor uses advanced capacitive touch and takes a high-resolution image from the “sub-epidermal layers” of skin, a process that, theoretically, should render a fake fingerprint useless. Starbug speculates that this is due to Apple's desire for usability over security, noting that the sensor will be defeated if the fake fingerprint is "sufficiently close" to the characteristics of human tissue.
Since its release, Touch ID has been the subject of much scrutiny. Senator Al Franken has sent a letter to Tim Cook asking a number of questions about the security of the system and the exact fingerprint storage process, and Apple has published an extensive knowledge base article about the benefits of the Touch ID system to alleviate some consumer concerns.






















