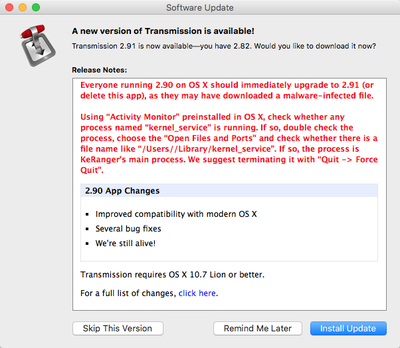
Over the weekend, the first instance of Mac ransomware was found in a malicious update to the Transmission BitTorrent client. Version 2.90 of Transmission downloaded from the Transmission website was infected with "KeRanger" ransomware.
"Ransomware" is a class of malware that encrypts a user's hard drive and files, demanding money to decrypt it. In this case, KeRanger would have required Mac users to shell out a bitcoin for decryption, equivalent to approximately $400.
The developers behind Transmission have shared some additional details on the attack with Reuters, giving us some insight into how it occurred. The server that delivers the Transmission software to customers was breached in a cyber attack, allowing the KeRanger malware to be added to the disk-image of its software.
Transmission representative John Clay told Reuters via email that the ransomware was added to disk-image of its software after the project's server was compromised in a cyber attack.
"We're not commenting on the avenue of attack, other than to say that it was our main server that was compromised," he said. "The normal disk image (was) replaced by the compromised one."
During the time that the malware-infected version of Transmission was available, it was downloaded approximately 6,500 times before the vulnerability was discovered. Security on the server has since been increased, ensuring a similar attack can't occur a second time.
On Sunday, Transmission's developers released software updates to block the malicious software and to remove it from the Macs of users who had unwittingly installed the malicious version. Apple also updated its software protections to keep the malware from affecting Mac users and to prevent the bad version from being installed on additional machines.
Customers who have downloaded the Transmission BitTorrent client should make sure they have updated the software to version 2.92, which will remove the malware from infected computers. Additional details on how to determine if you have the malware installed are available through Palo Alto Networks.