Security Researchers Don't Think Apple Pays Enough for Bug Bounties
Apple's bug bounty program has been available to select security researchers for almost a year now, but according to a new report from Motherboard, most researchers prefer not to share bugs with Apple due to low payouts. More money can be obtained from third-party sources for bugs in Apple software.
"People can get more cash if they sell their bugs to others," said Nikias Bassen, a security researcher for the company Zimperium, and who joined Apple's program last year. "If you're just doing it for the money, you're not going to give [bugs] to Apple directly."
Motherboard spoke to several members of Apple's bug bounty program with the condition of anonymity. Every single one said they had yet to report a bug to Apple and did not know anyone who had. iOS bugs are "too valuable to report to Apple," according to Patrick Wardle, a Synack researcher and former NSA hacker who was invited to the bug bounty program last year.
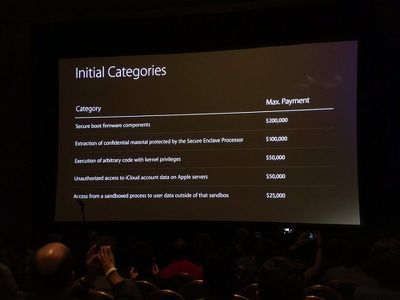
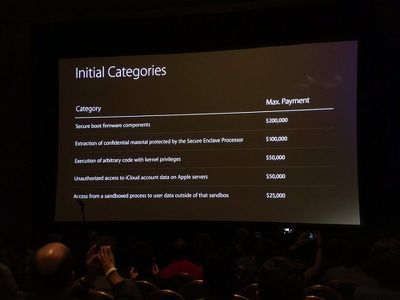
Apple first introduced its bug bounty program in August of 2016 at the Black Hat Conference, an annual global InfoSec event. Apple offers bounties of up to $200,000 depending on the vulnerability. Secure boot firmware components earn $200,000 at the high end, while smaller vulnerabilities, like access from a sandboxed process to user data outside of the sandbox, will earn $25,000.
Popular Stories
Apple today announced it will be permanently closing three retail stores in the U.S. in June, including Apple Trumbull in Trumbull, Connecticut, Apple North County in Escondido, California, and Apple Towson Town Center in Towson, Maryland.
Apple Towson Town Center in Maryland
Apple issued the following statement to MacRumors:At Apple, we are constantly striving to deliver exceptional service...
Apple today released a minor iOS 26.4.1 update for the iPhone 11 and newer. While the release notes for the update only mention unspecified "bug fixes," we have since learned about two specific changes that are included in it.
First, 9to5Mac spotted an Apple Developer Forums thread suggesting that iOS 26.4.1 fixes an iOS 26.4 bug that affected iCloud syncing in some apps.
Second, an...
As we wait for WWDC to kick off next Monday, Apple today announced the winners of its annual Apple Design Awards, recognizing apps and games for their innovation, ingenuity, and technical achievement.
The 2025 Apple Design Award winners are listed below, with one app and one game selected per category:
Delight and Fun - CapWords (App) and Balatro (Game)
Innovation - Play (App) and PBJ -...
Popular Stories
Anthropic on Tuesday announced Project Glasswing, a new initiative that will enable tech companies to use its new AI model Mythos Preview to find and fix security vulnerabilities or weaknesses across operating systems and web browsers.
Mythos Preview has already found thousands of zero-day vulnerabilities, including some in every major operating system and web browser, according to...
Apple says it has no record of a successful spyware attack against any device running Lockdown Mode, the opt-in security feature it introduced in 2022.
"We are not aware of any successful mercenary spyware attacks against a Lockdown Mode-enabled Apple device," an Apple spokesperson told TechCrunch.
Lockdown Mode is available on the iPhone, iPad, and Mac, and dramatically restricts...
Apple has begun pushing Lock Screen notifications to iPhones and iPads running older versions of iOS and iPadOS, warning users of active web-based attacks.
The alerts, which appear as a "Critical Software" notification from the Settings app, warn that Apple "is aware of attacks targeting out-of-date iOS software, including the version on your iPhone," and urge users to install a critical...