Apple's top security chief told the U.S. Congress on Sunday that it had found no indication of suspicious transmissions or other evidence that its China supply chain was ever compromised (via Reuters).
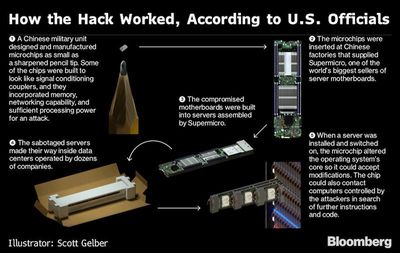
In a letter to the Senate and House commerce committees, Apple Vice President for Information Security George Stathakopoulos wrote that the company had repeatedly investigated and found no evidence to support Bloomberg Businessweek's bombshell report that alleged tiny chips were discovered inside Apple servers which allowed for backdoor transmissions to Chinese spies.
"Apple's proprietary security tools are continuously scanning for precisely this kind of outbound traffic, as it indicates the existence of malware or other malicious activity. Nothing was ever found," he wrote in the letter provided to Reuters.
Stathakopoulos repeated Apple's statements to the press that it had never found any such planted chips or been contacted by the FBI over the alleged matter. The letter follows a statement issued on Saturday by the U.S. Department of Homeland Security saying it had no reason to doubt the companies who denied that they had ever discovered the tiny chips.
Apple, Amazon, and Supermicro all strongly rebutted the report, which alleged that Chinese intelligence planted microchips in Supermicro servers, which Apple and Amazon previously used in their data centers.
Despite the denials, which are also backed by the UK's national cyber security agency, retired Apple general counsel Bruce Sewell, and other unnamed Apple senior executives, Bloomberg said it stood by its report as of Friday, but didn't immeditately respond to requests for comment on Sunday.
Note: Due to the political nature of the discussion regarding this topic, the discussion thread is located in our Politics, Religion, Social Issues forum. All forum members and site visitors are welcome to read and follow the thread, but posting is limited to forum members with at least 100 posts.





















