Developer Felix Krause today shared a proof of concept phishing attack that's gaining some traction as it clearly demonstrates how app developers can use Apple-style popups to gain access to an iPhone user's Apple ID and password.
As Krause explains, iPhone and iPad users are accustomed to official Apple requests for their Apple ID and password for making purchases and accessing iCloud, even when not in the App Store or iTunes app.
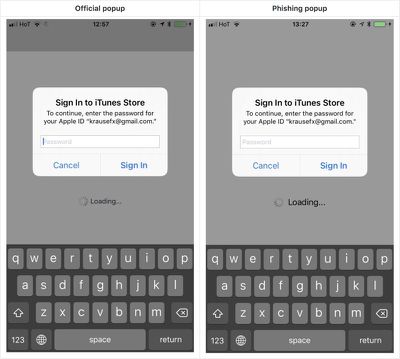
Using a UIAlertController that emulates the design of the system request for a password, developers can create an identical interface as a phishing tool that can fool many iOS users.
Showing a dialog that looks just like a system popup is super easy, there is no magic or secret code involved, it's literally the examples provided in the Apple docs, with a custom text.
I decided not to open source the actual popup code, however, note that it's less than 30 lines of code and every iOS engineer will be able to quickly build their own phishing code.
Though some of the system alerts would require a developer to have a user's Apple ID email address, there are also popup alerts that do not require an email and can recover a password.
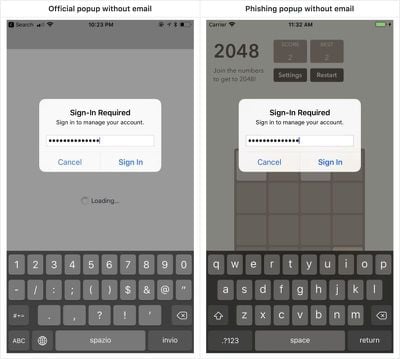
The phishing method that Krause describes is not new, and Apple vets apps that are accepted to the App Store, but it's worth highlighting for iOS users who may not be aware that such a phishing attempt is possible.
As Krause says, users can protect themselves by being wary of these popup dialogues. If one pops up, press the Home button to close the app. If the popup goes away, it's tied to the app and is a phishing attack. If it remains, it's a system request from Apple.
Krause also recommends users dismiss popups and enter their credentials directly within the Settings app.
Krause has reported the issue to Apple and recommends a fix that would include Apple asking customers to enter their credentials into the Settings app rather than directly through a popup that can be easily mimicked. Alternatively, he suggests credential requests could include an app icon to indicate that an app is asking rather than the system.
As extra protection from attacks like this, Apple customers should enable two-factor authentication as it prevents attackers from being able to log into an Apple ID account without a code from a verified device.























