Antivirus Firms Release Free Tools for Cleaning Macs Infected by Flashback
Yesterday, Apple disclosed for the first time that it is working to develop a software tool to detect and remove the Flashback malware from infected machines. We also previously profiled Flashback Checker, a simple app designed to allow users to easily see if their Macs are infected but which provides no assistance with disinfection.
While Apple works on its own official solution, other parties have continued to develop their own increasingly user-friendly tools for dealing with the threat and cleaning infected machines, with some of those tools making their way into the public's hands.
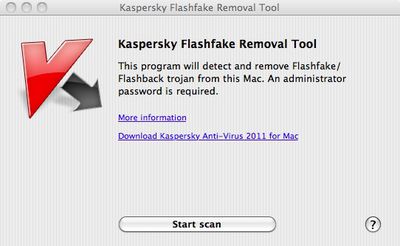
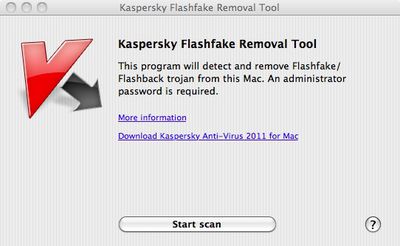
Russian antivirus firm Kaspersky Lab, which has played a key role in monitoring and publicizing the threat of Flashback, yesterday announced the launch of a free web-based checker where users can simply input the hardware UUID of their Mac to see if it has registered on the firm's servers as an infected machine. The company has also released Flashfake Removal Tool, a free app that quickly and easily detects and removes the malware.
Antivirus firm F-Secure has also announced its own free Flashback Removal app. The app generates a log file detailing whether it has found Flashback on a user's system, and if so quarantines it inside an encrypted ZIP file for disposal.
F-Secure also points out that Apple has yet to offer any protection for users running systems earlier than Mac OS X Snow Leopard. Flashback uses a vulnerability in Java to install itself without user authorization, and Apple released software patches for Java on Lion and Snow Leopard last week to close that hole and prevent infection on updated systems. Machines running earlier versions of Mac OS X do, however, remain unprotected. Specifically, F-Secure notes that over 16% of Macs are still running Mac OS X 10.5 Leopard, marking a substantial user base that remains vulnerable to the threat.
Update: Kaspersky Lab has informed MacRumors that the Flashfake Removal Tool has temporarily been pulled after the discovery that in some cases it could erroneously remove certain user settings. A fixed version of the tool will be posted as soon as it is available.
Update 2: The patched version of the Flashfake Removal Tool is now available through the Kaspersky Lab site.
Popular Stories
Apple will launch its new iPhone 17 series in two months, and the iPhone 17 Pro models are expected to get a new design for the rear casing and the camera area. But more significant changes to the lineup are not expected until next year, when the iPhone 18 models arrive.
If you're thinking of trading in your iPhone for this year's latest, consider the following features rumored to be coming...
In select U.S. states, residents can add their driver's license or state ID to the Wallet app on the iPhone and Apple Watch, providing a convenient and contactless way to display proof of identity or age at select airports and businesses, and in select apps.
Unfortunately, this feature continues to roll out very slowly since it was announced in 2021, with only nine U.S. states, Puerto Rico,...
Since the iPhone X in 2017, all of Apple's highest-end iPhone models have featured either stainless steel or titanium frames, but it has now been rumored that this design decision will be coming to an end with the iPhone 17 Pro models later this year.
In a post on Chinese social media platform Weibo today, the account Instant Digital said that the iPhone 17 Pro models will have an aluminum...
Three out of four iPhone 17 models will feature more RAM than the equivalent iPhone 16 models, according to a new leak that aligns with previous rumors.
The all-new iPhone 17 Air, the iPhone 17 Pro, and the iPhone 17 Pro Max will each be equipped with 12GB of RAM, according to Fixed Focus Digital, an account with more than two million followers on Chinese social media platform Weibo. The...
Apple is expanding the ability to add an Apple Account Card to the Wallet app to more countries, according to backend Apple Pay changes.
With iOS 15.5, Apple updated the Wallet app to allow users to add an Apple Account Card, which displays the Apple credit balance associated with an Apple ID.
If you receive an Apple gift card, for example, it is added to an Apple Account that is also...
Apple does not plan to refresh any Macs with updated M5 chips in 2025, according to Bloomberg's Mark Gurman. Updated MacBook Air and MacBook Pro models are now planned for the first half of 2026.
Gurman previously said that Apple would debut the M5 MacBook Pro models in late 2025, but his newest report suggests that Apple is "considering" pushing them back to 2026. Apple is now said to be...
Apple is continuing to refine and update iOS 26, and beta three features smaller changes than we saw in beta 2, plus further tweaks to the Liquid Glass design. Apple is gearing up for the next phase of beta testing, and the company has promised that a public beta is set to come out in July.
Transparency
In some apps like Apple Music, Podcasts, and the App Store, Apple has toned down the...
If you pay for iCloud storage on your iPhone, did you know that Apple offers you five perks beyond the extra storage space, at no additional cost?
Here are the perks included with all iCloud+ plans:Private Relay keeps your Safari browsing history entirely private from network providers, websites, and even Apple.
Hide My Email generates unique, random email addresses whenever needed.
Hom...