A security researcher was able to breach the internal systems of over 35 major companies, including Apple, Microsoft, and PayPal, using a software supply chain attack (via Bleeping Computer).
Security researcher Alex Birsan was able to exploit a unique design flaw in some open-source ecosystems called "dependency confusion" to attack the systems of companies such as Apple, Microsoft, PayPal, Shopify, Netflix, Yelp, Tesla, and Uber.
The attack involved uploading malware to open source repositories including PyPI, npm, and RubyGems, which were then automatically distributed downstream into the various companies' internal applications. Victims automatically received the malicious packages, with no social engineering or trojans required.
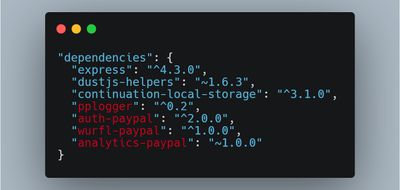
Birsan was able to create counterfeit projects using the same names on open-source repositories, each containing a disclaimer message, and found that applications would automatically pull public dependency packages, without needing any action from the developer. In some cases, such as with PyPI packages, any package with a higher version would be prioritized regardless of wherever it was located. This enabled Birsan to successfully attack the software supply chain of multiple companies.
Upon verifying that his component had successfully infiltrated the corporate network, Birsan reported his findings to the company in question, and some rewarded him with a bug bounty. Microsoft awarded him its highest bug bounty amount of $40,000 and released a white paper on this security issue, while Apple told BleepingComputer that Birsan will receive a reward via the Apple Security Bounty program for responsibly disclosing the issue. Birsan has now earned over $130,000 through bug bounty programs and pre-approved penetration testing arrangements.
A full explanation of the methodology behind the attack is available at Alex Birsan's Medium page.




















