Apple Tells Congress 'Nothing Was Ever Found' to Suggest Alleged Supply Chain-Based Hack
Apple's top security chief told the U.S. Congress on Sunday that it had found no indication of suspicious transmissions or other evidence that its China supply chain was ever compromised (via Reuters).
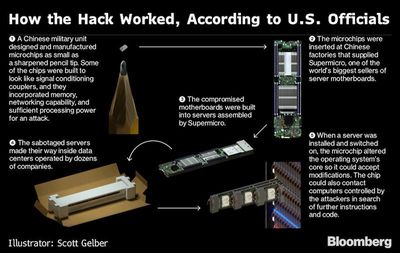
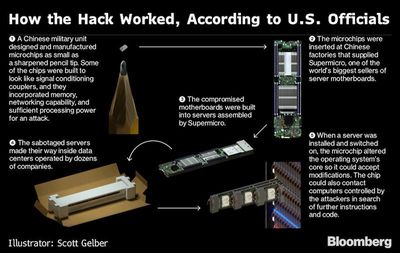
In a letter to the Senate and House commerce committees, Apple Vice President for Information Security George Stathakopoulos wrote that the company had repeatedly investigated and found no evidence to support Bloomberg Businessweek's bombshell report that alleged tiny chips were discovered inside Apple servers which allowed for backdoor transmissions to Chinese spies.
"Apple's proprietary security tools are continuously scanning for precisely this kind of outbound traffic, as it indicates the existence of malware or other malicious activity. Nothing was ever found," he wrote in the letter provided to Reuters.
Stathakopoulos repeated Apple's statements to the press that it had never found any such planted chips or been contacted by the FBI over the alleged matter. The letter follows a statement issued on Saturday by the U.S. Department of Homeland Security saying it had no reason to doubt the companies who denied that they had ever discovered the tiny chips.
Apple, Amazon, and Supermicro all strongly rebutted the report, which alleged that Chinese intelligence planted microchips in Supermicro servers, which Apple and Amazon previously used in their data centers.
Despite the denials, which are also backed by the UK's national cyber security agency, retired Apple general counsel Bruce Sewell, and other unnamed Apple senior executives, Bloomberg said it stood by its report as of Friday, but didn't immeditately respond to requests for comment on Sunday.
Note: Due to the political nature of the discussion regarding this topic, the discussion thread is located in our Politics, Religion, Social Issues forum. All forum members and site visitors are welcome to read and follow the thread, but posting is limited to forum members with at least 100 posts.
Popular Stories
The long wait for an Apple Watch Ultra 3 appears to be nearly over, and it is rumored to feature both satellite connectivity and 5G support.
Apple Watch Ultra's existing Night Mode
In his latest Power On newsletter, Bloomberg's Mark Gurman said that the Apple Watch Ultra 3 is on track to launch this year with "significant" new features, including satellite connectivity, which would let you...
Apple's next-generation iPhone 17 Pro and iPhone 17 Pro Max are just over two months away, and there are plenty of rumors about the devices.
Below, we recap key changes rumored for the iPhone 17 Pro models.
Latest Rumors
These rumors surfaced in June and July:Apple logo repositioned: Apple's logo may have a lower position on the back of the iPhone 17 Pro models, compared to previous...
The iPhone 17 Pro Max will feature the biggest ever battery in an iPhone, according to the Weibo leaker known as "Instant Digital."
In a new post, the leaker listed the battery capacities of the iPhone 11 Pro Max through to the iPhone 16 Pro Max, and added that the iPhone 17 Pro Max will feature a battery capacity of 5,000mAh:
iPhone 11 Pro Max: 3,969mAh
iPhone 12 Pro Max: 3,687mAh...
The upcoming iPhone 17 Pro and iPhone 17 Pro Max are rumored to have a slightly different MagSafe magnet layout compared to existing iPhone models, and a leaked photo has offered a closer look at the supposed new design.
The leaker Majin Bu today shared a photo of alleged MagSafe magnet arrays for third-party iPhone 17 Pro cases. On existing iPhone models with MagSafe, the magnets form a...
Apple's position as the dominant force in the global true wireless stereo (TWS) earbud market is expected to continue through 2025, according to Counterpoint Research.
The forecast outlines a 3% year-over-year increase in global TWS unit shipments for 2025, signaling a transition from rapid growth to a more mature phase for the category. While Apple is set to remain the leading brand by...
iOS 26 and iPadOS 26 add a smaller yet useful Wi-Fi feature to iPhones and iPads.
As spotted by Creative Strategies analyst Max Weinbach, sign-in details for captive Wi-Fi networks are now synced across iPhones and iPads running iOS 26 and iPadOS 26. For example, while Weinbach was staying at a Hilton hotel, his iPhone prompted him to fill in Wi-Fi details from his iPad that was already...
Apple today seeded the second betas of upcoming iOS 18.6 and iPadOS 18.6 updates to public beta testers, with the betas coming just a day after Apple provided the betas to developers. Apple has also released a second beta of macOS Sequoia 15.6.
Testers who have signed up for beta updates through Apple's beta site can download iOS 18.6 and iPadOS 18.6 from the Settings app on a compatible...