Over the course of the last month, some troubling information has surfaced about Ring, the Amazon-owned company that has millions of cameras inside and outside homes across the globe.
The Information in December suggested Ring employees in both the U.S. and the UK had unfettered, unnecessary access to customer camera feeds, and today, The Intercept has shared additional details.
Starting in 2016, Ring allowed its Ukraine-based research team to access "every video created by every Ring camera around the world." Video content was unencrypted and "easily browsed and viewed," plus videos were linked to specific customers.
Ring's Ukraine team was provided with access to further development on facial and object recognition software, with executives and engineers in the U.S. also able to access the same data even if they didn't specifically need it for their jobs.
Employees with access to customer feeds could view an individual's camera with just an email address.
Although the source said they never personally witnessed any egregious abuses, they told The Intercept "I can say for an absolute fact if I knew a reporter or competitor's email address, I could view all their cameras."
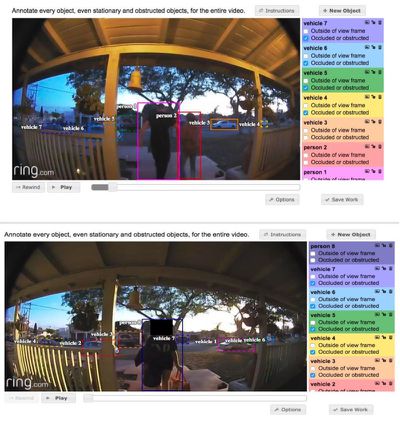
Ring employees weren't just watching outdoor video, either, with a source who spoke to The Intercept suggesting indoor video was viewed as well for the same object recognition training. Ring employees were instructed to draw boxes around objects with labeling, allowing the system to learn to recognize various things.
Employees allegedly showed each other the videos they were annotating and discussed some of the incidents they witnessed, such as people kissing, stealing, and guns being fired.
According to The Intercept, Ring is still using similar tactics for improving video tagging and object recognition. Ring Labs, the team Ring has in the Ukraine, is continuing to employ people who watch and tag details in Ring video content.
Ring spokesperson Yassi Shahmiri declined to answer The Intercept's questions about past and current data policies, but he confirmed that Ring views and annotates "certain Ring videos" that are either public or obtained with "explicit written consent."
We take the privacy and security of our customers' personal information extremely seriously. In order to improve our service, we view and annotate certain Ring videos. These videos are sourced exclusively from publicly shared Ring videos from the Neighbors app (in accordance with our terms of service), and from a small fraction of Ring users who have provided their explicit written consent to allow us to access and utilize their videos for such purposes.
Team members are held to "high ethical standards" and there are systems in place to "restrict and audit access to information." Bad actors are subject to a "zero tolerance" response if abuse is detected.
As The Intercept points out, given the information from the sources it spoke to, it is not known if Ring has always used the standards described in its current statement, and past reporting from The Information has suggested that access used to be less restrictive until Amazon purchased the service.
As Ring says, Ring users who are opting into the Neighbors system, which allows for sharing of videos to "create safer videos" are unknowingly opting in to potentially having those videos viewed by Ring employees and there is no mention of that when customers sign up for the feature.
Ring's terms of service and privacy policy do not mention manual or visual annotation by employees, even though that practice is still being used to this day, nor are customers notified that some employees had or could still have access to their camera feeds. Current and prospective Ring customers should be aware of Ring's practices and wary of who has access to their videos.
Update: A Ring spokesperson has provided the following updated statement to MacRumors on the situation:
"We take the privacy and security of our customers’ personal information extremely seriously. In order to improve our service, we view and annotate certain Ring video recordings. These recordings are sourced exclusively from publicly shared Ring videos from the Neighbors app (in accordance with our terms of service), and from a small fraction of Ring users who have provided their explicit written consent to allow us to access and utilize their videos for such purposes. Ring employees do not have access to livestreams from Ring products.
We have strict policies in place for all our team members. We implement systems to restrict and audit access to information. We hold our team members to a high ethical standard and anyone in violation of our policies faces discipline, including termination and potential legal and criminal penalties. In addition, we have zero tolerance for abuse of our systems and if we find bad actors who have engaged in this behavior, we will take swift action against them."






















