Apple today released Security Update 2017-001 to fix a serious vulnerability that enables access to the root superuser account with a blank password on any Mac running macOS High Sierra version 10.13.1.
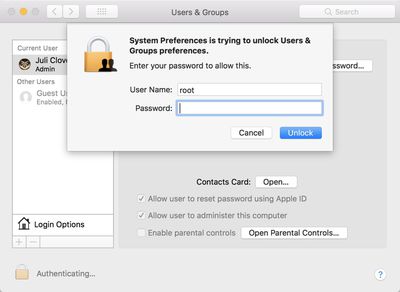
The critical bug, which gained attention after it was tweeted by developer Lemi Ergin yesterday, lets anyone gain administrator privileges by simply entering the username "root" and a blank password in System Preferences > Users & Groups.
The security update is rolling out on the Mac App Store now, and it should be installed by all users running macOS High Sierra as soon as possible. Regardless, starting later today, Apple said the security update will be automatically installed on all Macs running macOS High Sierra 10.13.1.
Apple has since apologized for the vulnerability in a statement issued to MacRumors:
Security is a top priority for every Apple product, and regrettably we stumbled with this release of macOS.
When our security engineers became aware of the issue Tuesday afternoon, we immediately began working on an update that closes the security hole. This morning, as of 8 a.m., the update is available for download, and starting later today it will be automatically installed on all systems running the latest version (10.13.1) of macOS High Sierra.
We greatly regret this error and we apologize to all Mac users, both for releasing with this vulnerability and for the concern it has caused. Our customers deserve better. We are auditing our development processes to help prevent this from happening again.
The vulnerability does not affect macOS Sierra or any other previous version of the operating system.

















