A number of Mac apps failed to launch for users over the weekend because of a change to the way Apple certifies apps that have not been bought directly from the Mac App Store.
Several users of apps including Soulver and PDFPen who had downloaded the apps from the developers' websites all reported immediate crashes on launch. Developers of the apps quickly apologized and said that the issue was down to the apps' code signing certificates reaching their expiration date.
Apple issues developer signing certificates to assure users that an app they have downloaded outside of the Mac App Store is legitimate, comes from a known source, and hasn't been modified since it was last signed. In the past, the expiration of a code signing certificate had no effect on already shipped software, but that changed last year, when Apple began requiring apps to carry something called a provisioning profile.
A provisioning profile tells macOS that the app has been checked by Apple against an online database and is allowed to perform certain system actions or "entitlements". However, the profile is also signed using the developer's code signing certificate, and when the certificate expires, the provisioning profile becomes invalid.
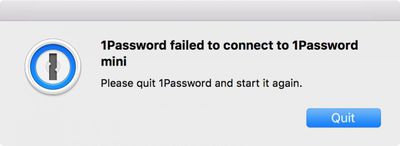
Victims of expired provisioning profiles over the weekend included users of 1Password for Mac who had bought the app from the developer's website. AgileBits explained on Sunday that affected users would need to manually update to the latest version (6.5.5), noting that those who downloaded 1Password from the Mac App Store were unaffected. The developers' surprise was explained in a blog post:
We knew our developer certificate was going to expire on Saturday, but thought nothing of it because we believed those were only necessary when publishing a new version. Apparently that's not the case. In reality it had the unexpected side effect of causing macOS to refuse to launch 1Password properly.
Currently, the common factor among affected apps appears to be those that were issued iCloud entitlements as part of their provisioning profile. Smile, developers of PDFpen and PDFpenPro, told TidBITS that users would need to manually download the latest updates to the apps to fix the problem.
Acqualia, developers of number-crunching app Soulver, also apologized for the problem and asked affected users to download an update to fix the issue.
As the above suggests, the immediate solution for developers with potentially affected apps is to renew their code signing certificates before they expire. AgileBits said the incident had given them "a new understanding of the importance of expiring provisioning profiles and certificates" and would be renewing its current certificate, due to expire in 2022, "far before then".



















