Apple is exploring ways to make information sharing between wearables and mobile devices as simple as a wave of the hand, if a new patent application is anything to go by (via AppleInsider).
Published by the U.S. Patent and Trademark Office, an Apple filing for "Gesture-based information exchange between devices in proximity" describes a secure data transfer system between two portable devices that works by detecting customizable gestures, or "greeting events", such as handshakes, high-fives, hugs, fist bumps, bows, waves, and salutes.
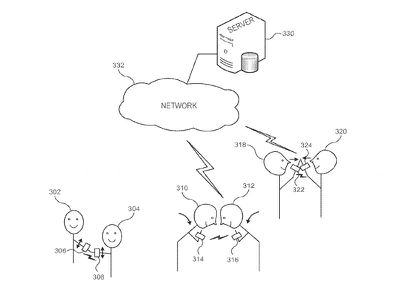
The gestures trigger a customizable data set that takes into account device context, with a particular focus on privacy and security. For example, in all cases, users must select the pre-defined gestures to allow the transfer of specific information only between the two devices, reducing the possibility of unintentionally sharing data with other devices in close proximity.
Information shared can be stored either locally or in the cloud, and can include most data fit for transfer across a wireless connection, such as contact details, photos, media files, calendar events, and so on. Greeting events can also generate data for sharing across social media, such as a Twitter post that announces a meeting between two users.
The sophisticated customization features of the system are of particular note, since they allow users to decide beforehand what kind of information is shared, and with whom, based on pre-defined contextual parameters, such as encountering someone for the first time, versus meeting a family member or an old friend. Device identifiers, location data, and user histories are all corralled in order to enhance the reliability and security of the system.
On another security note, the patent describes the use of cryptographic keys to identify individual sharing sessions, which can be either automated or user-initiated via an on-screen interface, with the possibility of using artificial intelligence-managed sharing under the hood.
As always with patents, the invention may or may not be used in-house or in a product, but the document offers another example of Apple's commitment to simplifying close-proximity data sharing while also paying particular attention to the security and privacy implications of such systems.




















Top Rated Comments
:Erases enemy's device: