With social media account hacking becoming increasingly more widespread, users would do well to make sure they're taking every security measure available to them. That goes doubly for frequenters of Facebook-owned Instagram, where account hijacking in particular is a recurring problem.

One of the best ways to protect any online account is by using two-factor authentication (2FA). 2FA offers hardened security during login attempts by requesting that the user provides an extra piece of information only they would know, such as a randomly generated code from a third-party.
Instagram has supported two-factor authentication for some time, but it was tied to a phone number and required users to receive text messages, which has proven to be insecure and left some Instagram users vulnerable to SIM hacking. More recently, Instagram added non SMS-based two-factor authentication to the app with support for third-party authenticator apps.
With 2FA enabled, you'll be the only person who can access your Instagram account from another device, regardless of whether someone learns your password as the result of a hack or a phishing scam, so it's well worth taking the time to enable the feature. This article shows you how. Note that you'll need to download an authenticator app to follow the steps below – we'll be using Google Authenticator, but Authy is another tried and tested option that works equally well.
How to Protect Your Instagram Account With 2FA
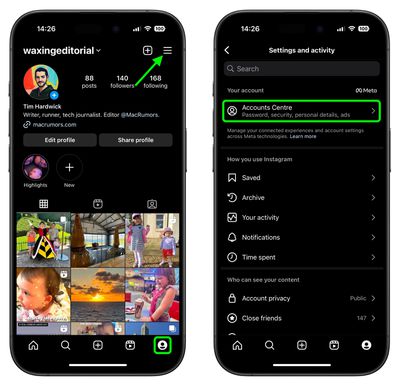
- Launch the Instagram app on your iPhone and log in to your account if you aren't already.
- Tap the Profile icon in the bottom-right corner, then tap the More (three lines) icon in the top-right corner of your profile.
- Tap Accounts Center.

- Under "Account settings," tap Password and security.
- Tap Two-factor authentication.
- Tap Get started at the bottom.

As you follow the on-screen instructions for setting up two-factor authentication on Instagram, you'll be asked to choose one of two security methods: Authentication app or Text Message. For the best security, choose Authentication. After you've turned on two-factor authentication, you'll be able to see login requests and remove trusted devices.
And that's it – 2FA is now enabled for your Instagram account. Note that once you've authenticated a trusted device in this way, you won’t have to do it every time you launch the app, but your account will remain protected.
























Top Rated Comments
https://motherboard.vice.com/en_us/article/5984zn/listen-to-sim-jacking-account-ransom-instagram-email-tmobile
https://www.wired.com/2016/06/hey-stop-using-texts-two-factor-authentication/
That was 2 years ago, and the attacks have only gotten easier to pull off. I know someone who makes their living on IG, and this was one of their biggest fears. Finally adding a secure 2FA method is a big deal.
https://krebsonsecurity.com/2018/08/reddit-breach-highlights-limits-of-sms-based-authentication/