A vulnerability affecting iOS 13.3.1 and later prevents virtual private networks (VPNs) from encrypting all traffic, allowing some internet connections to bypass encryption, potentially exposing users' data and IP addresses.
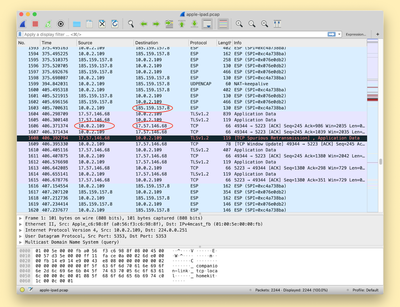
Details on the vulnerability were shared today by Bleeping Computer after it was discovered by ProtonVPN. The vulnerability is caused because iOS isn't terminating all existing connections when a user connects to a VPN, allowing them to reconnect to destination servers once the VPN tunnel has been established.
Connections made after connecting to a VPN on an iOS are not affected by this bug, but all previously established connections are not secure. This could potentially lead to a user who believes they are protected accidentally exposing IP an address and therefore, an approximate location.
Apple's Push Notifications are cited as an example of a process using connections on Apple's servers that aren't closed automatically when connecting to a VPN, but it can affect any app or service running on a user's device.
VPNs cannot work around the issue because iOS does not allow VPN apps to kill existing network connections, so this is a fix that will need to be implemented by Apple. Apple is aware of the vulnerability and is looking into options to mitigate it.
Until fixed, VPN users can connect to a VPN server, turn on Airplane Mode and then turn off Airplane Mode to kill all existing connections. The mitigation isn't entirely reliable, however, so iPhone and iPad owners who rely on VPNs should be careful until Apple puts out a fix.