Flashback Malware's Ad-Click Hijacking Detailed, Could Reap $10,000/Day
Antivirus firm Symantec has published a new blog post examining how the Flashback malware affecting hundreds of thousand of Macs has been generating revenue for its authors by hijacking users' ad clicks. According to the report, the widespread nature of the infection means that malware authors could have been generating up to $10,000 per day from the scheme at its peak based on previous analysis of malware click redirection.
The Flashback ad-clicking component is loaded into Chrome, Firefox, and Safari where it can intercept all GET and POST requests from the browser. Flashback specifically targets search queries made on Google and, depending on the search query, may redirect users to another page of the attacker's choosing, where they receive revenue from the click . (Google never receives the intended ad click.)
Symantec's work on the ad-click hijacking aspect of Flashback comes after Russian firm Dr. Web, which was responsible for the initial publicity about the malware, published its own report examining some of the early data on infected computers seeking to connect to command-and-control servers.
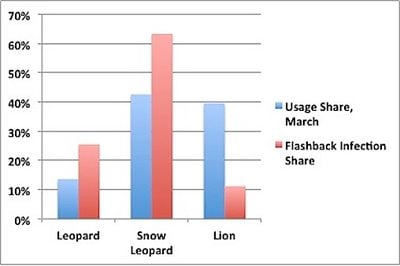
The report looks at nearly 100,000 connections that came in on April 13, finding that close to two-thirds of the infected machines identified themselves as running Mac OS X Snow Leopard, which was the last version of OS X to ship with Java enabled by default. OS X Lion does not include Java by default, and thus was responsible for only 11% of infections seen during the survey period.
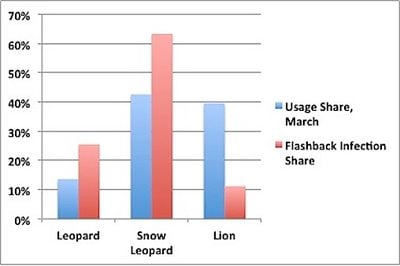 Flashback infection share vs. operating system usage share (Data via Dr. Web, Chart via Computerworld)
Flashback infection share vs. operating system usage share (Data via Dr. Web, Chart via Computerworld)As
noted by Computerworld, OS X Lion represents nearly 40% of OS X copies currently in use, suggesting that Apple's decision to remove Java from the default Lion install is indeed helping to limit infections on Apple's newest machines.
[W]hile Snow Leopard's and Leopard's infection rates are higher than their usage shares, the opposite's true of OS X 10.7, or Lion. The 2011 OS accounted for 39.6% of all copies of OS X used last month, yet represented only 11.2% of the Flashback-compromised Macs.
Dr. Web's data on OS kernel versions being reported from infected Macs also demonstrates that many Mac users do not keep their systems up-to-date, with roughly 25% of Snow Leopard and Lion systems seen in the survey reporting themselves as at least one version behind Apple's most recent updates (10.6.8 for Snow Leopard and 10.7.3 for Lion).
Popular Stories
As we wait for WWDC to kick off next Monday, Apple today announced the winners of its annual Apple Design Awards, recognizing apps and games for their innovation, ingenuity, and technical achievement.
The 2025 Apple Design Award winners are listed below, with one app and one game selected per category:
Delight and Fun - CapWords (App) and Balatro (Game)
Innovation - Play (App) and PBJ -...
Last year, Apple launched CarPlay Ultra, the long-awaited next-generation version of its CarPlay software system for vehicles. Nearly a year later, CarPlay Ultra is still limited to Aston Martin's latest luxury vehicles, but that should change fairly soon.
In May 2025, Apple said many other vehicle brands planned to offer CarPlay Ultra, including Hyundai, Kia, and Genesis.
CarPlay Ultra...
Apple's iPhone development roadmap runs several years into the future and the company is continually working with suppliers on several successive iPhone models at the same time, which is why we often get rumored features months ahead of launch. The iPhone 18 series is no different, and we already have a good idea of what to expect for the iPhone 18 Pro and iPhone 18 Pro Max.
One thing worth...
Popular Stories
As we wait for WWDC to kick off next Monday, Apple today announced the winners of its annual Apple Design Awards, recognizing apps and games for their innovation, ingenuity, and technical achievement.
The 2025 Apple Design Award winners are listed below, with one app and one game selected per category:
Delight and Fun - CapWords (App) and Balatro (Game)
Innovation - Play (App) and PBJ -...
Last year, Apple launched CarPlay Ultra, the long-awaited next-generation version of its CarPlay software system for vehicles. Nearly a year later, CarPlay Ultra is still limited to Aston Martin's latest luxury vehicles, but that should change fairly soon.
In May 2025, Apple said many other vehicle brands planned to offer CarPlay Ultra, including Hyundai, Kia, and Genesis.
CarPlay Ultra...
Apple's iPhone development roadmap runs several years into the future and the company is continually working with suppliers on several successive iPhone models at the same time, which is why we often get rumored features months ahead of launch. The iPhone 18 series is no different, and we already have a good idea of what to expect for the iPhone 18 Pro and iPhone 18 Pro Max.
One thing worth...