German security researcher Linus Henze this week discovered a new zero-day macOS vulnerability dubbed "KeySteal," which, as demoed in the video below, can be used to get to all of the sensitive data stored in the Keychain app.
Henze appears to use a malicious app to extract data from the Mac's Keychain app without the need for administrator access or an administrator password. It can get passwords and other information from Keychain, as well as passwords and details for other macOS users.
Henze has not shared the details of this exploit with Apple and says that he won't release it because Apple has no bug bounty program available for macOS. "So blame them," Henze writes in the video's description. In a statement to Forbes, Henze clarified his position, and said that discovering vulnerabilities takes time.
"Finding vulnerabilities like this one takes time, and I just think that paying researchers is the right thing to do because we're helping Apple to make their product more secure."
Apple has a reward program for iOS that provides money to those who discover bugs, but there is no similar payment system for macOS bugs.
According to German site Heise Online, which spoke to Henze, the exploit allows access to Mac Keychain items but not information stored in iCloud. Keychain is also required to be unlocked, something that happens by default when a user logs in to their account on a Mac.
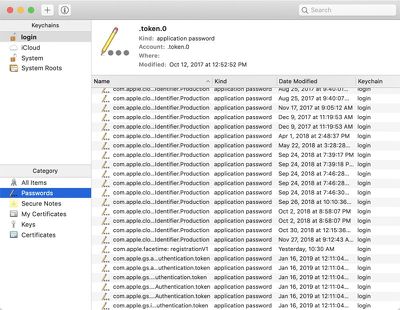
Keychain can be locked by opening up the Keychain app, but an admin password then needs to be entered whenever an application needs to access Keychain, which can be inconvenient.
Apple's security team has reached out to Henze, according to ZDNet, but he has continued to refuse to provide additional detail unless they provide a bug bounty program for macOS. "Even if it looks like I'm doing this just for money, this is not my motivation at all in this case," said Henze. "My motivation is to get Apple to create a bug bounty program. I think that this is the best for both Apple and Researchers."
This isn't the first Keychain-related vulnerability discovered in macOS. Security researcher Patrick Wardle demoed a similar vulnerability in 2017, which has been patched.