Late last week, CNET reported on a new trojan horse threat targeting Mac users. While the threat was initially discovered back in late July and had yet to become fully functional, only recently was the malware highlighted by antivirus companies targeting such threats.
The new threat consists of two parts, with the first being a trojan downloader known as "OSX/Revir.A" that serves to distract users by downloading and continually opening a PDF document containing "offensive political statements" written in Chinese. But the actual damage from OSX/Revir.A comes as it installs a backdoor known as OSX/Imuler.A to potentially allow malicious parties to access the user's machine.
When the backdoor is installed, it will set up a launch agent on the system that is used to continually keep the malware active on the system. It will then connect to a remote server and send the system's current username and MAC address to the server, after which the server will instruct it to either archive files and upload them, or take screenshots and upload them to the server.
The report noted that the malware did not appear to function properly due to a lack of instructions being delivered from a remote server, but malicious activity could still be possible.
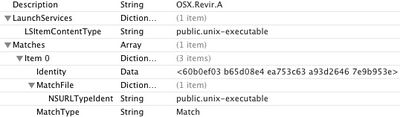
OS X malware definition entry for OSX/Revir.A
Apple has moved quickly to counter the threat, updating its malware definitions for Snow Leopard and Lion systems to allow them to recognize the trojan. Apple updated its tools earlier this year in response to the MacDefender threat, and Snow Leopard and Lion systems now automatically check for new malware definitions on a daily basis.
Apple's battles with malware authors continue, however, as CNET discloses that another trojan horse, known as OSX/flashback.A, has been discovered. Like a similar threat that surfaced early last month, the new trojan masquerades as a Flash Player installer to trick users into installing the package.
Unlike the previous Flash Trojan (called Bash/QHost.WB), which changed one file on the system, this new Trojan is a bit more complex and first deactivates network security features, then installs a dyld library that will run and inject code into applications that the user is running. The Trojan will also try to send personal information and machine-specific information to remote servers.
Users requiring Adobe's Flash Player software are of course advised to download it directly from Adobe's site rather than attempting to install it from sites which may be trying to trick users into installing malware. If past history is any indication, Apple should quickly update its malware definitions to help recognize the new threat, alerting users to the known malicious nature of the package should they attempt to download and install it.