Apple to Address '0.0.0.0' Security Vulnerability in Safari 18
Apple plans to block websites from attempting to send malicious requests to the IP address 0.0.0.0 on macOS Sequoia, according to Forbes. The means the change will be part of Safari 18, which will also be available for macOS Sonoma and macOS Ventura.

This decision comes after researchers from Israeli cybersecurity startup Oligo Security said they discovered a zero-day security vulnerability that allows a malicious actor to access private data on a user's internal private network. The researchers will present their findings this weekend at the DEF CON hacking conference in Las Vegas.
"Exploiting 0.0.0.0-day can let the attacker access the internal private network of the victim, opening a wide range of attack vectors," said Avi Lumelsky, a researcher at Oligo Security.
The researchers responsibly disclosed the vulnerability to Apple, Google, and Mozilla. More details are available on the AppSec Village website.
macOS Sequoia and Safari 18 are currently in beta and will be widely released later this year.
Popular Stories
iOS 26.4 was released today, and it includes a couple of new features for CarPlay: an Ambient Music widget and support for voice-based chatbot apps.
To update your iPhone 11 or newer to iOS 26.4, open the Settings app and tap on General → Software Update. CarPlay will automatically offer the new features so long as the iPhone connected to your vehicle is running iOS 26.4 or later....
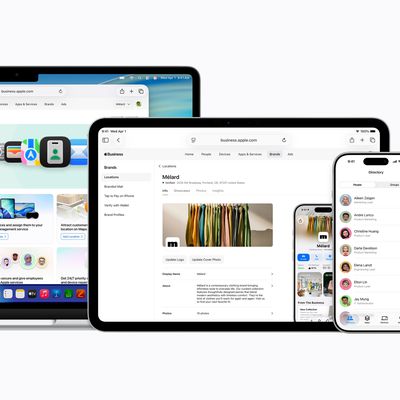
Apple today announced Apple Business, a new all-in-one platform that unifies device management, productivity tools, and customer outreach features.
The service is designed to be a consolidated replacement for several of Apple's existing business-focused offerings, including Apple Business Essentials, Apple Business Manager, and Apple Business Connect. It provides organizations with a single...
Apple today released new firmware for the AirPods Pro 2, AirPods Pro 3, and the AirPods 4. The firmware has a version number of 8B39, up from 8B34 on the AirPods Pro 3, 8B28 on the AirPods Pro 2, and 8B21 on the AirPods 4.
There is no word on what's included in the firmware, but Apple has a support document with limited notes. Most updates are limited to bug fixes and performance...
![]()