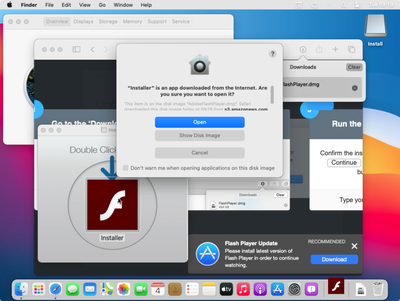
Apple mistakenly approved and notarized a common kind of malware for macOS on at least two occasions, reports TechCrunch.
Apple requires developers to submit their apps for security checks to run on macOS in a process called "notarization." Notarization was required from the launch of macOS Catalina. If software has not been notarized, it will be blocked by default in macOS.
Peter Dantini and security researcher Patrick Wardle at Objective-See report that they have found the first malware for Mac that has been successfully notarized by Apple, even for the latest beta version of macOS Big Sur. The notarized malware was disguised as an Adobe Flash installer, which is an oft-used technique to convince unknowing users to install a trojan.
It contained "Shlayer" malware, which is said to be the "most common threat" to Macs in 2019. Shlayer is a kind of adware that intercepts encrypted web traffic, even from securely-encrypted HTTPS-enabled websites, and replaces it with its own ads to raise fraudulent ad revenue.
The researchers believe that Apple cannot have detected the malicious code when it was submitted for approval. The discovery is particularly surprising, given that the malware and its vehicle are extremely common. Upon notification from the researchers, Apple revoked the notarization.
"Malicious software constantly changes, and Apple's notarization system helps us keep malware off the Mac and allow us to respond quickly when it's discovered. Upon learning of this adware, we revoked the identified variant, disabled the developer account, and revoked the associated certificates. We thank the researchers for their assistance in keeping our users safe," an Apple spokesperson told TechCrunch.
In spite of Apple's statement, the researchers reported that the bad actors were able to get yet another malware trojan notarized soon after. The second notarized payloads were still approved by Apple as of yesterday.
Earlier this month, a new kind of Mac malware was discovered that infects via Xcode and supposedly can infiltrate the Mac App Store, undetected by Apple.