A security researcher claims changes Apple made to tighten its kernel security system in iOS 7 instead weakened the system, making it less secure than its iOS 6 counterpart. (Via CNET and ThreatPost) Azimuth Security researcher Tarjei Mandt discovered the flaw and presented his findings last week at CanSecWest.
The security flaw involves the random number generator Apple uses to secure its kernel. In iOS 6, the number generator that encrypted the kernel derived its values in part from the CPU clock counter. Because it was based on time, the encryption was only marginally secure as the output values were predictable, especially when examining successive numbers.
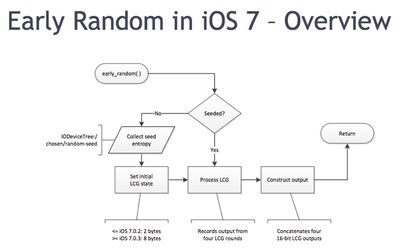
Apple was aware of the limitations in iOS 6 and attempted to tighten security in iOS 7 by changing the random number generator to a linear congruential generator, which is more susceptible to brute force attacks.
The problem with the new generator in iOS 7 is that it uses a linear recursion algorithm, Mandt said, which has "more correlation" between the values it generates. That makes them easier to extrapolate and guess, he said.
This flaw potentially allows a malicious hacker to gain kernel-level access to an iOS device via an unpatched vulnerability. The kernel is the base part of the iOS operating system and controls low-level functions such as security and resource allocation.
Apple approached Mandt about his findings and asked for his CanSecWest slide presentation.






















Top Rated Comments
Couldn't have been an accident that someone missed, could it? Nah....everyone get your tin foil hats out cause everyone's out to get us.
In reality, props to white-hat hackers like Mandt
No. Apple would never do this. They never compromise on customer security for anyone.
It's very hard to say how much of a problem there actually is. My understanding - which may be wrong - is that this random number generator is used at the very early stages while iOS is booting, and is then replaced with something a lot stronger. There's the claim that the random number sequence could be predicted, but then I wonder which non-Apple software would be running on the device at the early stages when this random number generator is in use. Quite possibly none at all.