A pair of vulnerabilities in the framework that some Mac apps use to receive automatic updates leaves them open to man-in-the-middle attacks, according to a report from Ars Technica covering a security flaw that was first discovered by a security researcher named Radek in late January.
Apps that use a vulnerable version of Sparkle and an unencrypted HTTP channel for server updates are at risk of being hijacked to transmit malicious code to end users. The Sparkle framework is used by apps outside of the Mac App Store to facilitate automatic software updates.
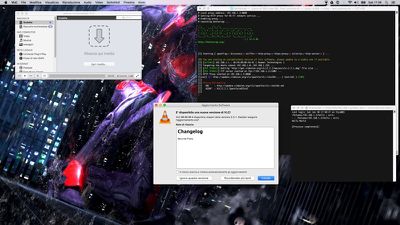
Some of the affected apps are widely downloaded titles like Camtasia, Duet Display, uTorrent, and Sketch. A proof of concept attack was shared by Simone Margaritelli using an older version of VLC, which was recently updated to patch the flaw. The vulnerabilities were tested on both OS X Yosemite and the most recent version of OS X El Capitan.
A "huge" number of apps are said to be at risk, but as Ars Technica points out, it is difficult to tell exactly which apps that use Sparkle are open to attack. GitHub users have compiled a list of apps that use Sparkle, but not all use the vulnerable version and not all transfer data over non-secured HTTP channels.
Apps downloaded through the Mac App Store are not affected as OS X's built in software update mechanism does not use Sparkle.
Sparkle has released a fix in the newest version of the Sparkle Updater, but it will take some time for Mac apps to implement the patched framework. Ars Technica recommends concerned users with potentially vulnerable apps installed avoid using unsecured Wi-Fi networks or do so only via a VPN.






















