iOS developer Daniel Amitay today took an interesting look (via The Next Web) at iPhone passcode trends as revealed by usage of his popular Big Brother Camera Security application.
In my last update to Big Brother Camera Security (Free), I added some code to record common user passcodes (completely anonymous, of course). Because Big Brother's passcode setup screen and lock screen are nearly identical to those of the actual iPhone passcode lock, I figured that the collected information would closely correlate with actual iPhone passcodes.
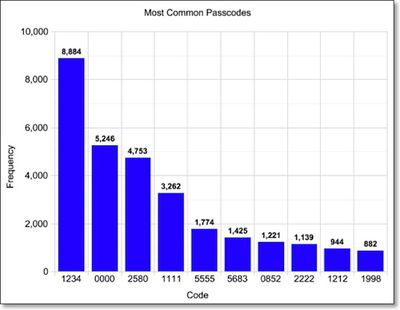
Perhaps unsurprisingly, the most popular passcode for the app was "1234", a choice made by about 4.3% of users. Other popular codes include ones with repeating numbers (such as "0000" and "1111") and patterns on the keypad (such as "2580" and "1212"). All told, Amitay discovered that 15% of the over 200,000 passcodes captured by his app were represented by just ten different passcodes.
The implication? A thief (or just a prankster) could safely try 10 different passcodes on your iPhone without initiating the data wipe. With a 15% success rate, about 1 in 7 iPhones would easily unlock--even more if the intruder knows the users' years of birth, relationship status, etc.
Beyond the passcodes representing repetitive and patterned entries, Amitay found a higher-than-expected frequency of passcodes in the 1980-2000 range, suggesting that users are prone to using their birth years or years of other significant events in their lives as their passcodes.























Top Rated Comments
Of course that means that once in a while my passcode is 1234 or 0000! :eek:
:D :D
You owe me a keyboard to replace the one I've just spurted coffee all over! ;)
4263=hand
:p