Last week, Russian anti-virus firm Doctor Web disclosed a newly discovered piece of OS X malware known as Mac.BackDoor.iWorm that at the time had affected roughly 17,000 machines around the world. While the exact mechanism of infection was unclear, an interesting twist to the story involves compromised machines running search queries on Reddit to obtain instructions about which command and control servers should be used to manage the botnet.
It is worth mentioning that in order to acquire a control server address list, the bot uses the search service at reddit.com, and -- as a search query -- specifies hexadecimal values of the first 8 bytes of the MD5 hash of the current date. The reddit.com search returns a web page containing a list of botnet C&C servers and ports published by criminals in comments to the post minecraftserverlists under the account vtnhiaovyd.
Once connected to a command and control server, the backdoor opened by the malware on the user's system can receive instructions to perform a variety of tasks, from stealing sensitive information to receiving or spreading additional malware.
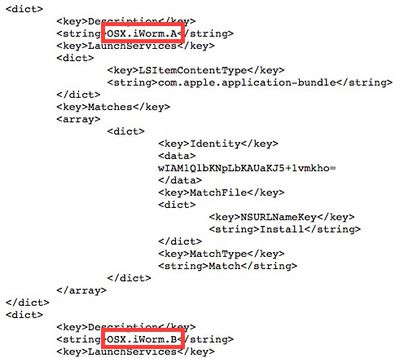
In an effort to address the threat, Apple has now updated its "Xprotect" anti-malware system to recognize two different variants of the iWorm malware and prevent them from being installed on users' machines.
First introduced with OS X Snow Leopard, Xprotect is a rudimentary anti-malware system that recognizes and alerts users to the presence of various types of malware. Given the relative rarity of malware targeting OS X, the malware definitions are updated infrequently, although users' machines automatically check for updates on a daily basis. Apple also uses the Xprotect system on occasion to enforce minimum version requirements for plug-ins such as Flash Player and Java, forcing users to upgrade from older versions known to carry significant security risks.






















