The Next Web is reporting that a group of iOS developers has been targeted with a series of rapid-fire messages on iMessage, creating a sort of denial-of-service (DoS) attack that crashes the iMessage app.
Grant Paul, one of the targeted iOS developers explains how the attack worked:
“What’s happening is a simple flood: Apple doesn’t seem to limit how fast messages can be sent, so the attacker is able to send thousands of messages very quickly,” Paul says.
The second part of that, he explains, is that if a user sends a ‘complex’ text message using unicode characters that force a browser to render ‘Zalgo’ text, or simply uses a message that is enormous in size, them the Messages app will eventually crash as it fails to display it properly. This will effectively ‘break’ the Messages app on iOS by forcing it to close and stop it from re-opening because it can’t render that text.”
iH8sn0w, an iOS jailbreak tool and app developer, showed TNW a proof-of-concept AppleScript that would be able to create the barrage of iMessages. A potential spammer would only need a person's email address and the AppleScript to engage in the attack, especially after Apple unified phone numbers and email addresses in iOS 6. 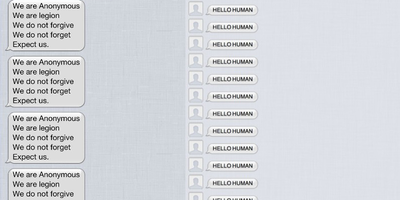
Currently, there is no way to block particular senders in iMessage, though iH8sn0w said it should be possible for Apple to notice the bursts of messages and block them as repetitive spamming. Victims can also disable iMessage entirely.
It's not clear who initiated the attack, nor why these developers were targeted, though it appears the attacks are merely a prank.























Top Rated Comments
This comment wins for most ridiculous comment I have ever seen on Macrumors and that's saying something.
How do you people think this %!?# up?
Why does it have to be from the "hackintosh community"? Anyone can carry out this iMessage attack its so simple.
To send an iMessage:
Step 1: Type your message and hit send
Step 2: Put your thumb in the middle of the screen to scan your print
Step 3: Type captcha image
Step 4: Say your verification phrase
Step 5: Take selfie of yourself for face verification
Step 6: Offer 1oz. of blood for dna verifications
Step 7: Repeat until you die of blood loss.
Read the story man. It tells you who did it.
I even quoted it.