iOS Vulnerability Prevents VPNs From Encrypting All Traffic
A vulnerability affecting iOS 13.3.1 and later prevents virtual private networks (VPNs) from encrypting all traffic, allowing some internet connections to bypass encryption, potentially exposing users' data and IP addresses.
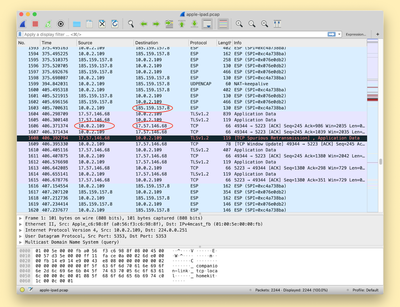
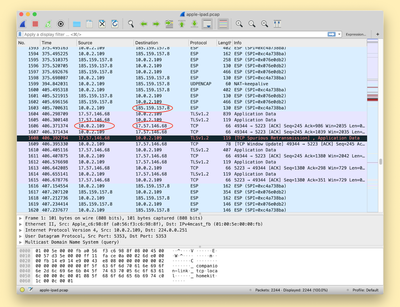
A screenshot from ProtonVPN demonstrating exposed connections to Apple's servers that should be protected by the VPN
Details on the vulnerability were shared today by Bleeping Computer after it was discovered by ProtonVPN. The vulnerability is caused because iOS isn't terminating all existing connections when a user connects to a VPN, allowing them to reconnect to destination servers once the VPN tunnel has been established.
Connections made after connecting to a VPN on an iOS are not affected by this bug, but all previously established connections are not secure. This could potentially lead to a user who believes they are protected accidentally exposing IP an address and therefore, an approximate location.
Apple's Push Notifications are cited as an example of a process using connections on Apple's servers that aren't closed automatically when connecting to a VPN, but it can affect any app or service running on a user's device.
VPNs cannot work around the issue because iOS does not allow VPN apps to kill existing network connections, so this is a fix that will need to be implemented by Apple. Apple is aware of the vulnerability and is looking into options to mitigate it.
Until fixed, VPN users can connect to a VPN server, turn on Airplane Mode and then turn off Airplane Mode to kill all existing connections. The mitigation isn't entirely reliable, however, so iPhone and iPad owners who rely on VPNs should be careful until Apple puts out a fix.
Popular Stories
Apple has announced it will be holding a special event on Tuesday, May 7 at 7 a.m. Pacific Time (10 a.m. Eastern Time), with a live stream to be available on Apple.com and on YouTube as usual. The event invitation has a tagline of "Let Loose" and shows an artistic render of an Apple Pencil, suggesting that iPads will be a focus of the event. Subscribe to the MacRumors YouTube channel for more ...
Apple has dropped the number of Vision Pro units that it plans to ship in 2024, going from an expected 700 to 800k units to just 400k to 450k units, according to Apple analyst Ming-Chi Kuo. Orders have been scaled back before the Vision Pro has launched in markets outside of the United States, which Kuo says is a sign that demand in the U.S. has "fallen sharply beyond expectations." As a...
Apple is finally planning a Calculator app for the iPad, over 14 years after launching the device, according to a source familiar with the matter. iPadOS 18 will include a built-in Calculator app for all iPad models that are compatible with the software update, which is expected to be unveiled during the opening keynote of Apple's annual developers conference WWDC on June 10. AppleInsider...
The upcoming iOS 17.5 update for the iPhone includes only a few new user-facing features, but hidden code changes reveal some additional possibilities. Below, we have recapped everything new in the iOS 17.5 and iPadOS 17.5 beta so far. Web Distribution Starting with the second beta of iOS 17.5, eligible developers are able to distribute their iOS apps to iPhone users located in the EU...
Apple today released several open source large language models (LLMs) that are designed to run on-device rather than through cloud servers. Called OpenELM (Open-source Efficient Language Models), the LLMs are available on the Hugging Face Hub, a community for sharing AI code. As outlined in a white paper [PDF], there are eight total OpenELM models, four of which were pre-trained using the...
Apple has stopped production of FineWoven accessories, according to the Apple leaker and prototype collector known as "Kosutami." In a post on X (formerly Twitter), Kosutami explained that Apple has stopped production of FineWoven accessories due to its poor durability. The company may move to another non-leather material for its premium accessories in the future. Kosutami has revealed...




















Top Rated Comments
iOS used to handle this correctly, then stopped.
Not tearing down existing connections completely undermines the point of a VPN.
TCP is designed to retry after being torn down. It’s no biggie.
The fact is, this is an iOS bug, which was introduced recently.
If a VPN is configured to send all network traffic through the VPN when it’s running - which is typically what‘s done - then all traffic should be routing through it from the moment it’s enabled. Not just connections to new end points established afterward - all traffic.
Even if a VPN is configured to just carry traffic to a few specific end points (such as the OpenVPN tunnel to our servers, which I’m relying on heavily right now due to the stay at home order currently in place here in Washington): if you’re already connected to one of those end points before establishing the tunnel, you would expect all further traffic to go through the tunnel. The idea that you wouldn’t is ludicrous.
There’s actually two types on iOS. Split vpn and full tunnel. Split allows some stuff to be routed elsewhere. Full tunnel tunnels everything.