Security Researchers Don't Think Apple Pays Enough for Bug Bounties
Apple's bug bounty program has been available to select security researchers for almost a year now, but according to a new report from Motherboard, most researchers prefer not to share bugs with Apple due to low payouts. More money can be obtained from third-party sources for bugs in Apple software.
"People can get more cash if they sell their bugs to others," said Nikias Bassen, a security researcher for the company Zimperium, and who joined Apple's program last year. "If you're just doing it for the money, you're not going to give [bugs] to Apple directly."
Motherboard spoke to several members of Apple's bug bounty program with the condition of anonymity. Every single one said they had yet to report a bug to Apple and did not know anyone who had. iOS bugs are "too valuable to report to Apple," according to Patrick Wardle, a Synack researcher and former NSA hacker who was invited to the bug bounty program last year.
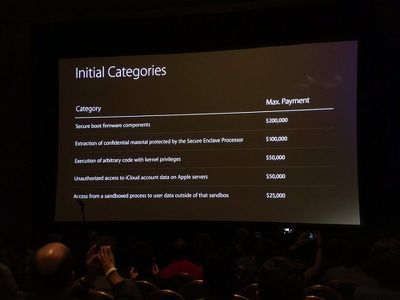
Apple first introduced its bug bounty program in August of 2016 at the Black Hat Conference, an annual global InfoSec event. Apple offers bounties of up to $200,000 depending on the vulnerability. Secure boot firmware components earn $200,000 at the high end, while smaller vulnerabilities, like access from a sandboxed process to user data outside of the sandbox, will earn $25,000.
Popular Stories
Game emulator apps have come and gone since Apple announced App Store support for them on April 5, but now popular game emulator Delta from developer Riley Testut is available for download. Testut is known as the developer behind GBA4iOS, an open-source emulator that was available for a brief time more than a decade ago. GBA4iOS led to Delta, an emulator that has been available outside of...
Last September, Apple's iPhone 15 Pro models debuted with a new customizable Action button, offering faster access to a handful of functions, as well as the ability to assign Shortcuts. Apple is poised to include the feature on all upcoming iPhone 16 models, so we asked iPhone 15 Pro users what their experience has been with the additional button so far. The Action button replaces the switch ...
A decade ago, developer Riley Testut released the GBA4iOS emulator for iOS, and since it was against the rules at the time, Apple put a stop to downloads. Emulators have been a violation of the App Store rules for years, but that changed on April 5 when Apple suddenly reversed course and said that it was allowing retro game emulators on the App Store. Subscribe to the MacRumors YouTube channel ...
The lead developer of the multi-emulator app Provenance has told iMore that his team is working towards releasing the app on the App Store, but he did not provide a timeframe. Provenance is a frontend for many existing emulators, and it would allow iPhone and Apple TV users to emulate games released for a wide variety of classic game consoles, including the original PlayStation, GameCube, Wii,...
The first approved Nintendo Entertainment System (NES) emulator for the iPhone and iPad was made available on the App Store today following Apple's rule change. The emulator is called Bimmy, and it was developed by Tom Salvo. On the App Store, Bimmy is described as a tool for testing and playing public domain/"homebrew" games created for the NES, but the app allows you to load ROMs for any...


















Top Rated Comments
For one, you might've been right if we were talking about security research from 20 years ago, when it wasn't taken so seriously. However, modern security research is a business in and of itself. It takes a lot of knowledge and training, but more importantly it takes resources. Most external security researchers will not have access to the source code of these applications or OS features that they are probing for vulnerabilities.
Most groups that actively search for vulnerabilities apply techniques like 'fuzzing' where they dedicate hardware to constantly throw input at an application or API until it breaks, and then the researcher figures out if that break is exploitable. These breaks appear in the forms of application crashes and kernel panics. Most kernel level vulnerabilities would sweep the top of the bounty range, since that would allow for access to a system beyond that of an administrator or super user. Getting back to the point, Apple Hardware does not exactly come cheap, and to compete with a lot of the top end researchers like Google's Project Zero, you're going to need a significant investment to even get started.
When any company considers how much to pay out, the company must analyze how frequently bugs are going to be discovered that are significant enough to be rewarded, how much a vulnerability in this particular application or device would be paid for to malicious actors, and what damage to the company would a complete outbreak of an exploit targeting your product would cause to the company's image. If vulnerabilities are going to be frequent, its best to not offer a bounty and to have a team work in-house to discover them - because you will be flooded by submissions from amateur researchers grabbing low-hanging fruit. If vulnerabilities are going to rare and deal high damage to the company's image, as is in Apple's case which champions their security, then the payout needs to be significant enough to compensate researchers for their investment of both time and resources.
I hope this clears things up for readers.
Facebook claimed their largest payout ever was just $33,500. A bug that was reported that could unlock any user's account received just $15,000.
Microsoft's top payout is $30,000 with Google (apps such as gmail or YouTube specifically, not Android) just slightly up from there at $31,337. Unrestricted file system access that can lead to a google account takeover receives a max of $13,337 from Google.
For the Android part of Google, the top amount is $150-200k which is more on par with Apple.
I think the underground market will always pay more no matter what price Apple sets.
guy, it shows your morality and that you couldn't care less....